Cybersecurity management consulting services are in high demand due to the increasing number of cyberattacks. These services help organizations assess their cybersecurity risks and develop strategies to mitigate them. Cybersecurity management consultants have expertise in a variety of areas, including information security, risk management, and incident response. By partnering with a reputable consulting firm, organizations can ensure that their cybersecurity programs are effective and up to date.
Cybersecurity management consulting services help organizations assess their security posture, identify gaps, and develop and implement strategies to improve their overall security. These services can supplement an organization’s internal resources or provide expertise in specific areas.
Common services include:
-Security program assessment and development
-Risk management
-Policy and procedures development
-Security awareness training
-Incident response planning
A good cybersecurity management consultant will have a deep understanding of security principles and practices and experience implementing security solutions in various environments. They will also be able to effectively communicate with all levels of an organization, from the C-suite to front-line employees.
Benefits: cybersecurity management consulting services
Cybersecurity management consulting services can help organizations assess their current security posture, identify gaps and make recommendations for improvement. In addition, these services can provide guidance on implementing security controls to protect against specific threats.
An effective cybersecurity management consulting engagement should result in an organization having a clear understanding of its risks and the steps it needs to take to mitigate those risks. The organization should also have a roadmap for implementing the recommended security controls.
Cybersecurity management consulting services can be an invaluable resource for organizations looking to improve their security posture. By working with an experienced consultant, organizations can get expert advice on how to protect their systems and data best.
Drawbacks: potential disadvantages of working with a consultant
There are several potential disadvantages of working with a consultant. One is that the consultant may not have the same level of knowledge or experience as an in-house cybersecurity specialist. Another potential disadvantage is that the consultant may not be familiar with the company’s systems and processes, which could lead to security vulnerabilities. Finally, consultants typically charge higher rates than in-house staff, which can be a significant cost for companies.
How to find a good consultant: tips for finding a reputable and qualified consultant
As technology advances, so do the strategies for protecting digital information. Businesses must be proactive in guarding against online threats such as cyberattacks, data breaches, and viruses. Many companies lack the internal resources to adequately address these issues, which is where cybersecurity management consulting services come in.
An experienced consultant can provide an objective assessment of a company’s security risks and vulnerabilities. They can also help develop and implement tailored security solutions that fit the specific needs of the business. Cybersecurity management consulting services can be a valuable investment for any organization that wants to protect its data and reputation.
Cybersecurity Management Consulting Services Market Expected to Grow Significantly During the Forecast Period 2022-2031
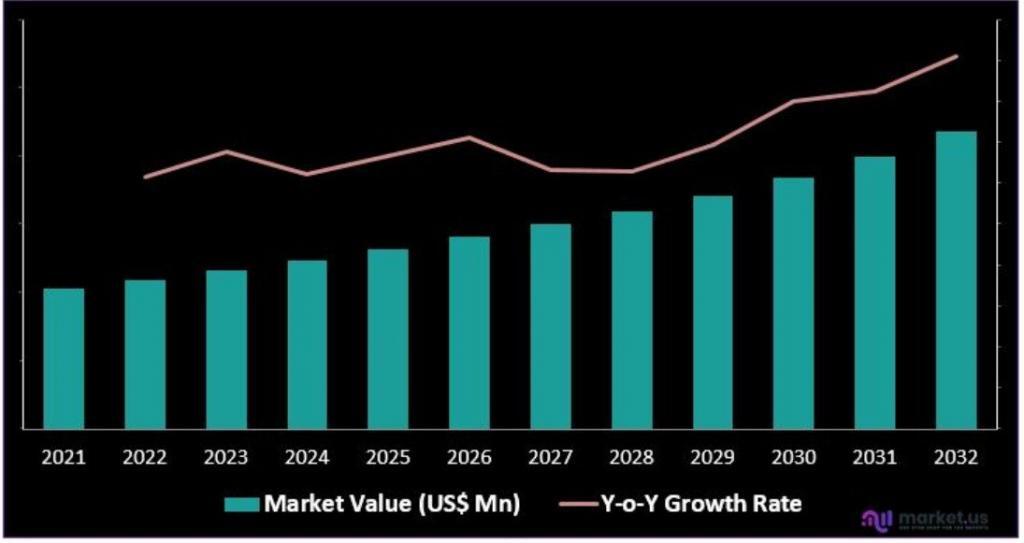
This growth is attributed to the increasing need for organizations to protect their data and infrastructure from cyberattacks. In addition, the growing trend of BYOD and IoT is also expected to contribute to the market’s growth.
The global cybersecurity management consulting services market is segmented by services, organization size, end-user, and geography. The market is further segmented by services: risk and compliance management, identity and access management, security operations, incident response, and others. The risk and compliance management services segment is expected to grow at the highest CAGR during the forecast period.
Market Scope:
By type, the market is segmented into Type I, and Type II. By application, the market is divided into Client’s Market Capitalization: 5000 Million, and Government.
Based on geography, the market is analyzed across North America, Europe, Asia-Pacific, Latin America, and Middle East and Africa. Major players profiled in the report include AT&T, TCS, Hewlett Packard Enterprise, PwC, Vumetric, Wipro, IT Governance, RSA, Telos, MARSH LLC. ALL RIGHTS RESERVED, AT&T Intellectual Property, SecureWorksInc., and Deloitte.
Top #5 Questions Ask by People
1. What are cybersecurity consulting services?
2. What does a security management consultant do?
3. How do IT consultants provide cybersecurity?
4. What do security consultants charge?
5. What are the top 3 interpersonal skills of a security consultant?
6. What is the role of a cyber security analyst?
Conclusion: are they worth the investment?
As the world becomes increasingly digital, the need for strong cybersecurity measures is more important than ever. Many businesses are turning to cybersecurity management consulting services to help them create a plan to protect their data and systems. But are these services worth the investment?
There are a few things to consider when determining if cybersecurity management consulting services are right for your business. First, consider the size and scope of your business and what kind of threats it faces. If you have a large and complex network, you may need more help protecting it than a small business with a simple system. Also, think about your budget and whether you can afford to hire a consultant or team of consultants.
Overall, cybersecurity management consulting services can be a valuable investment for businesses of all sizes. By working with an experienced consultant, you can create a comprehensive plan to keep your data safe from cyberattacks.
You may also want to read,